
VMware has published security updates to address a high severity vulnerability in vRealize Operations that could allow attackers to steal admin credentials after exploiting vulnerable servers.
vRealize Operations is an AI-powered and “self-driving” IT operations management for private, hybrid, and multi-cloud environments, available as an on-premises or SaaS solution.
The vulnerability was discovered and reported to VMware by Positive Technologies web security researcher Egor Dimitrenko.
SSRF exploitable by unauthenticated attackers
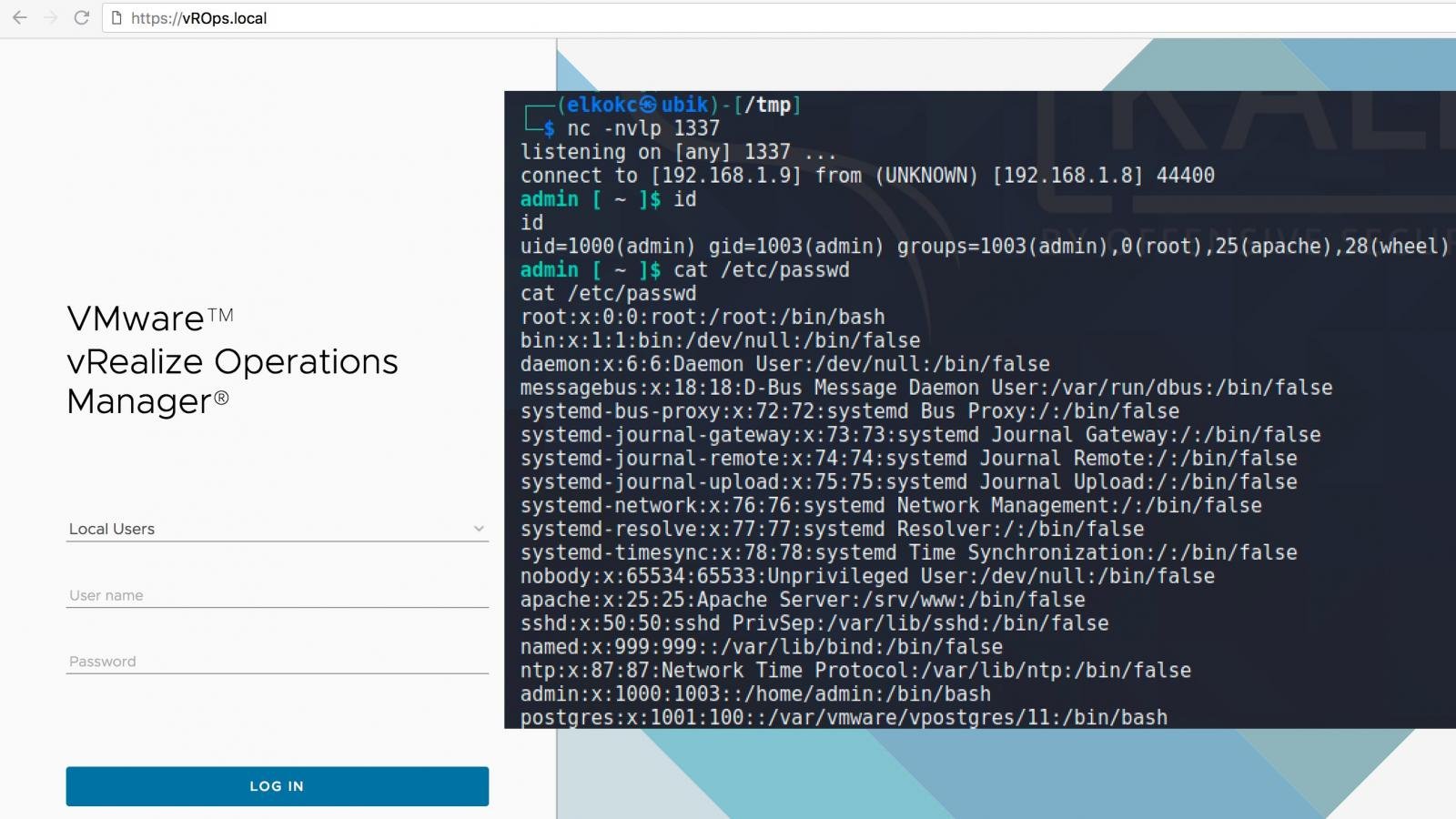
The privately reported vulnerability tracked as CVE-2021-21975 is caused by a Server Side Request Forgery bug in the vRealize Operations Manager API.
Attackers can exploit the vulnerability remotely without requiring authentications or user interaction in low complexity attacks to steal administrative credentials.
VMware rated the security flaw as high severity giving it a base score of 8.6 out of 10.
Details on how to get the security patch for vRealize Operations are available in the support articles linked below:
Workaround also available
VMware has also published workaround instructions for admins who don’t want to or can’t immediately patch servers running vulnerable vRealize Operations versions (e.g., there is no patch for their version).
As the company explained, there are is no impact after applying the workaround measures and no functionality will be affected.
To work around this issue, you will have to remove a configuration line from the casa-security-context.xml file and restart the CaSA service on the affected device.
Detailed information on how to do that is available in the support articles linked above for each security patch/version.
VMware today fixed a second high-severity vulnerability in the vRealize Operations Manager API (tracked as CVE-2021-21974) and allowing authenticated attackers to remotely “write files to arbitrary locations on the underlying photon operating system.”
When chained together, CVE-2021-21975 and CVE-2021-21983 lead to pre-auth remote code execution (RCE) on unpatched vRealize Operations servers.
