
A cryptocurrency platform was recently on the receiving end of one of the biggest distributed denial-of-service attacks ever after threat actors bombarded it with 15.3 million requests, content delivery network Cloudflare said.
DDoS attacks can be measured in several ways, including by the volume of data, the number of packets, or the number of requests sent each second. The current records are 3.4 terabits per second for volumetric DDoSes—which attempt to consume all bandwidth available to the target—809 million packets per second, and 17.2 million requests per second. The latter two records measure the power of application-layer attacks, which attempt to exhaust the computing resources of a target’s infrastructure.
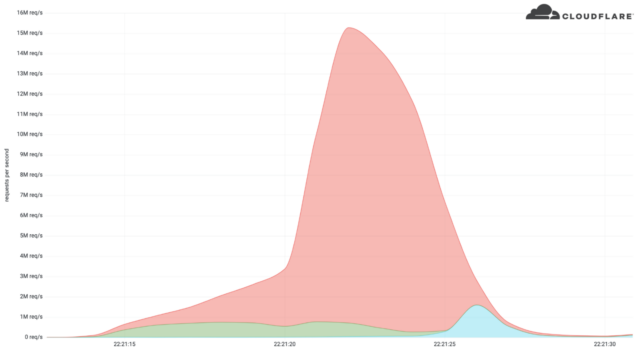
Cloudflare’s recent DDoS mitigation peaked at 15.3 million requests per second. While still smaller than the record, its power was more considerable because the attack was delivered through HTTPS requests rather than HTTP requests used in the record. Because HTTPS requests are much more compute-intensive than HTTP requests, the latest attack had the potential to put much more strain on the target.
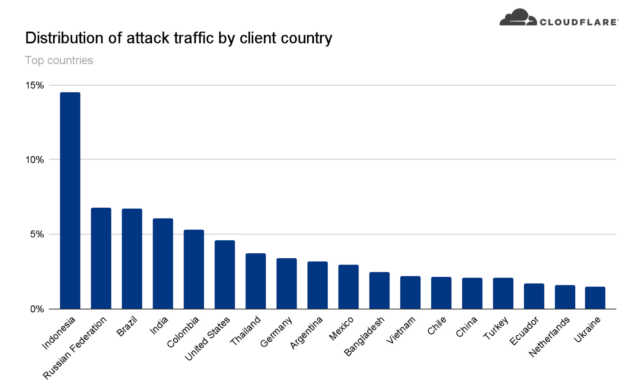
The resources required to deliver the HTTPS request flood were also greater, indicating that DDoSers are growing increasingly more powerful. Cloudflare said that the botnet responsible, comprising about 6,000 bots, has delivered payloads as high as 10 million requests per second. The attack originated from 112 countries, with about 15 percent of the firepower from Indonesia, followed by Russia, Brazil, India, Colombia, and the United States.
“Within those countries, the attack originated from over 1,300 different networks,” Cloudflare researchers Omer Yoachimik and Julien Desgats wrote. They said that the flood of traffic mainly came from data centers, as DDoSes move away from residential network ISPs to cloud computing ISPs. Top data center networks included the German provider Hetzner Online GmbH (Autonomous System Number 24940), Azteca Comunicaciones Colombia (ASN 262186), and OVH in France (ASN 16276). Other sources included home and small office routers.
“In this case, the attacker was using compromised servers on cloud hosting providers, some of which appear to be running Java-based applications. This is notable because of the recent discovery of a vulnerability (CVE-2022-21449) that can be used for authentication bypass in a wide range of Java-based applications,” Cloudflare VP of Product Patrick Donahue wrote in an email. “We also saw a significant number of MikroTik routers used in the attack, likely exploiting the same vulnerability that the Meris botnet did.”
The attack lasted about 15 seconds. Cloudflare mitigated it using systems in its network of data centers that automatically detect traffic spikes and quickly filter out the sources. Cloudflare didn’t identify the target except that it operated a crypto launchpad, a platform used to help fund decentralized finance projects.
The numbers underscore the arms race between attackers and defenders as each attempts to outdo the other. It won’t be surprising if a new record is set in the coming months.
