Security researchers piecing together evidence from multiple attacks on cryptocurrency exchanges, attributed to a threat actor they named CryptoCore have established a strong connection to the North Korean state-sponsored group Lazarus.
The group is believed to have stolen hundreds of millions of U.S. dollars by breaching cryptocurrency exchanges in the U.S., Israel, Europe, and Japan over the past three years.
Long-term money-making mission
Last year, cybersecurity company ClearSky published a report about the financially motivated CryptoCore campaign that targeted cryptocurrency wallets belonging to exchanges or their employees.
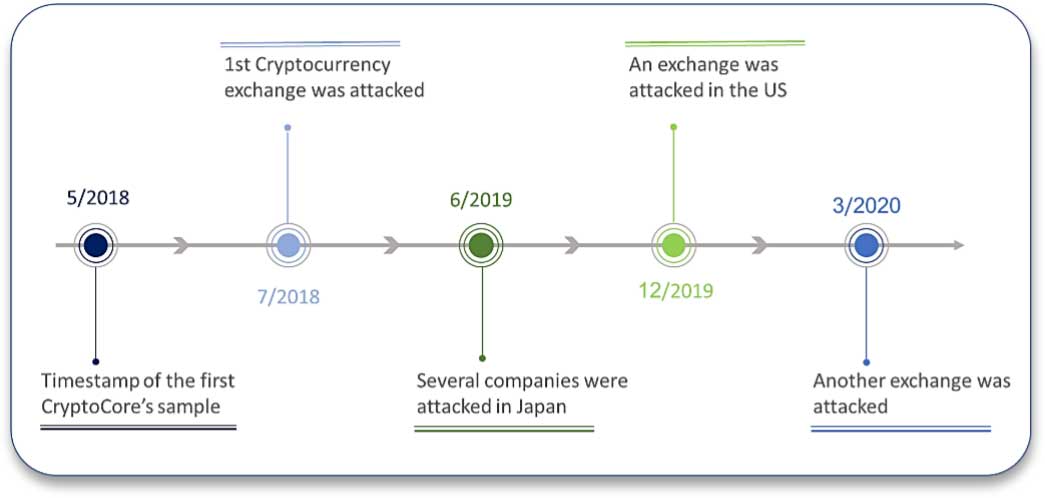
The campaign started in 2018 and relied on spear-phishing to gain an initial foothold. At the time of the report, CryptoCore was responsible for at least five attacks causing estimated losses of more than $200 million.
ClearSky believed that the threat actor was connected to hackers in Eastern European countries like Ukraine, Russia, and Romania.
Following ClearSky’s report, other cybersecurity organizations published results of their investigation of similar attacks and technical details that aligned to CryptoCore’s tactics, techniques, and procedures:
- A report from F-SECURE, which reviewed a large-scale, international campaign found while investigating attacks on crypto wallets. According to the research paper, the attackers started a conversation with their targets and convinced them to download a malicious file. The paper showed an analysis of the malware used in the attack and outlined similarities between them and malware attributed to LAZARUS.
- A report from Japan’s CERT JPCERT/CC, which shared an analysis of several incidents where employees of Japanese firms were contacted and convinced to download malicious files. The report offered no details about the affected parties but provided some technical information about the malware used in the attack.
- A report from the Japanese cybersecurity firm NTT SECURITY, which points to a campaign that they dubbed CRYPTOMIMIC. According to the report, large sums of money were stolen from crypto wallets by contacting users and convincing them to download malicious files. The report contained information about the attack’s modus operandi as well as a technical analysis of the malware used.
Matching tools and IoCs
In a new report today, ClearSky compared the details in these researches to their findings and noticed sufficient similarities to confidently attribute the attacks to the same actor.
It is important to note that ClearSky has accepted F-Secure’s attribution of the attacks to the Lazarus group after checking if the company’s YARA rules for identifying and classifying malware applied to remote access trojans (RATs) in reports about Lazarus from ESET and Kaspersky.
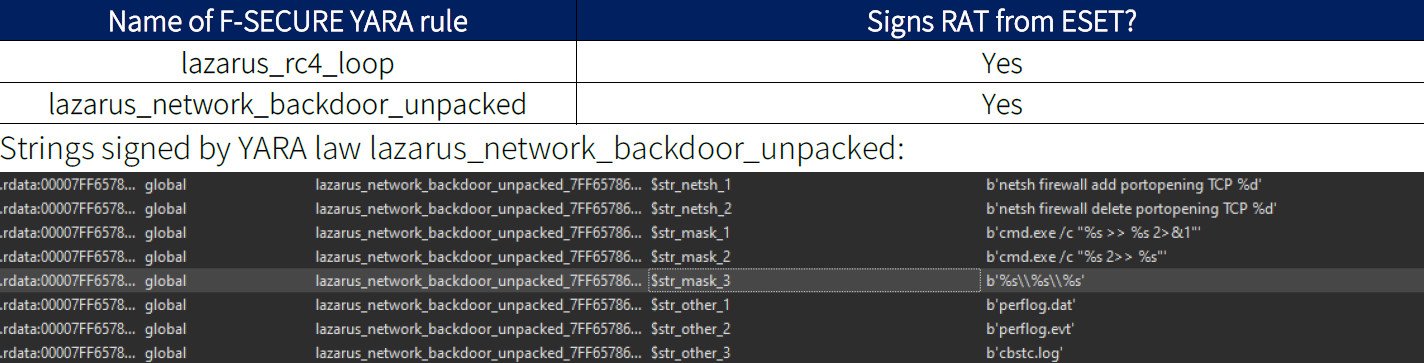
ClearSky notes that the YARA rule matched an old RAT that Kaspersky reported in 2016 (bbd703f0d6b1cad4ff8f3d2ee3cc073c). However, this was possible only after changing the name of a resource, which was different for the 2016 version of the backdoor.
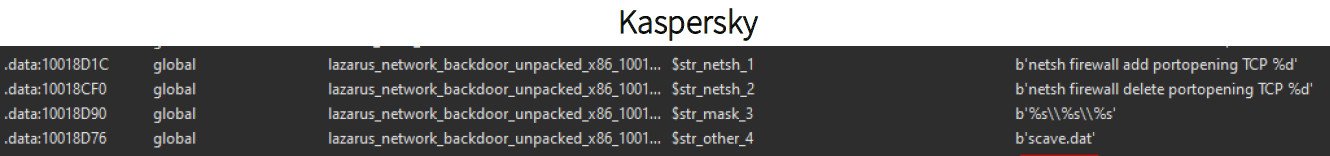
In the old variant, the malware accessed a file named “scaeve.dat,” while the newer one looked for “perflog.dat.” Changing the file name caused the YARA rule to find a match, though.
Between the reports from F-Secure, NTT Security, and JPCERT/CC, ClearSky found a total of 40 common indicators of compromise (IoCs), a VBS script that was almost identical when not obfuscated and matching RATs and stealers.

Given all the similarities across these researchers allowed ClearSky to attribute with medium to high confidence all the CryptoCore campaigns to the North Korean hacking group Lazarus.
The researchers also point out that the hackers have expanded their activity as they recently started to focus on Israeli targets. It may be that the hackers’ choice of victims is indiscriminate and their only criteria in selecting a target is for it to fit a financial profile.
