
The Microsoft Exchange admin portal is currently inaccessible from some browsers after Microsoft forgot to renew the SSL certificate for the website.
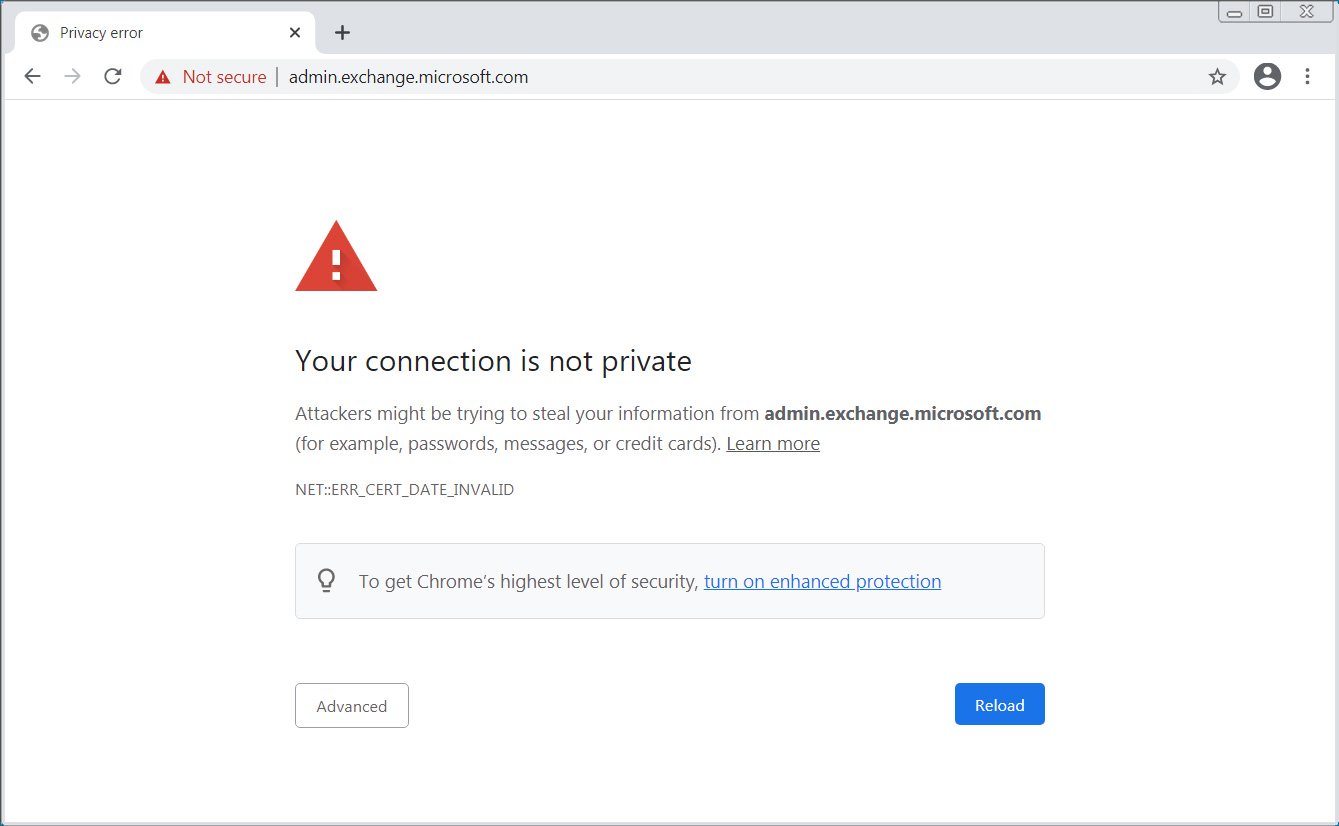
Starting at 8 AM EST today, Microsoft Exchange admins who attempted to access the admin portal at admin.exchange.microsoft.com suddenly found that their browsers were issuing warnings that the connection was not private due to an expired SSL certificate.
Depending on the browser, users are blocked from accessing the site as a security precaution or shown an alert that the data may not be secure. For example, Google Chrome will stop you from accessing the site altogether, while Firefox will warn you about the insecure connection.
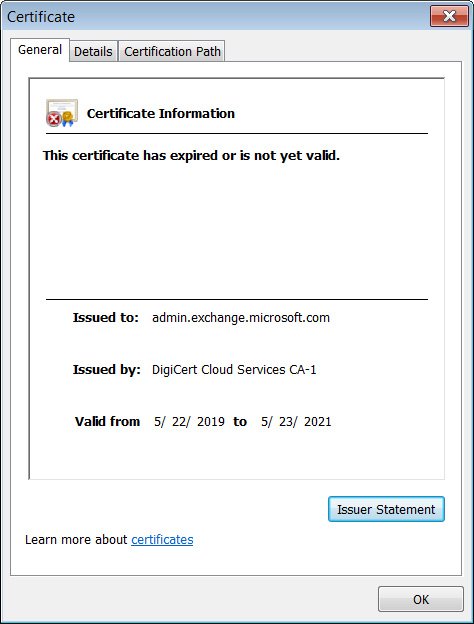
According to Qualys’ SSL Labs, the certificate expired today, Sun, 23 May 2021, at 12:00:00 UTC. For those on the east coast of the United States, that is is equivalent to Sun, 23 May 2021 08:00:00 EST.
Microsoft states that they are aware of the issue and are working on a fix.
We’ve isolated the problem and are applying a fix. Additional details can be found in the Service health dashboard under EX257883.
— Microsoft 365 Status (@MSFT365Status) May 23, 2021
As a temporary workaround, Microsoft states you can access the admin portal from the https://outlook.office.com/ecp/ URL as well.
Unfortunately, outages caused by expired certificates are becoming all too common as almost all online services have now switched over to secure connections.
With encrypted communications come additional complexity and human error, such as forgetting to renew an SSL certificate.
In August 2020, an expired certificate for California’s CalREDIE infectious disease reporting system led to an underreporting of COVID-19 cases in the state as data was prevented from being uploaded.
We have also seen expired SSL certificates affecting consumer-facing services, such as Spotify, Microsoft Teams, and Facebook’s Tor server.
BleepingComputer has reached out to Microsoft to learn more about when they expect the SSL certificate to be renewed but has not heard back at this time.
Update 5/24/21 08:10 AM EST: Microsoft states they resolved the issue yesterday afternoon and released the following final status:
We’ve completed applying the configuration fix on the affected authentication component, and after monitoring service telemetry, we confirmed that the issue is now fully resolved.
Thx to David for the tip!
